4. The ability to understand how online communication affects privacy and security
The Digital Literacy Framework Explored (with suggested activities and resources)
- Capacity to map and monitor digital footprints – ability to understand the nature and scope of a digital footprint and what online activity can tell others about ourselves
- Ability to identify platforms and techniques for safe digital communication – recognise the need for appropriate guidelines to maintain and enhance online privacy and security
This section introduces different kinds of communities, digital communities and explores ‘speaking out’ in this context.
Case studies: #ToxicTwitter; #breakingstereotypes
Key Questions
- What is a digital footprint and why is it important?
- How can we be private and safe on the internet?
- How can we prevent our data and information from being used without us knowing?
Activity 4. 1 Exploring why privacy matters
1. Ask your group to name some occasions when privacy is important to them (at home, at school or work, in public) and use the answers to develop a definition of privacy. Then, do the same exercise again, this time focusing on security – if they are unsure about the concept of security, ask them to think about times when it feels important to be kept safe or have information about themselves, the family and friends and their personal belongings kept safe.
Note that when they use the internet or any digital media, it is important to keep privacy and security in mind; this is because they leave a digital footprint – something that can easily compromise their and other’s security and privacy. They may not want other individuals, organisations or companies to be able to access their information or that of friends and family. Such information can be used for reasons they might not be happy with. The information can also often be sold by online companies to others or used for political reasons with which they do not agree.
2. Give each smaller group a copy of the guidelines to think about and discuss.
- Handout 10: guidelines
Ask them to think about the following questions:
- What is the reason for having guidelines such as this?
- What are some things that could happen if you follow these guidelines?
- What are some things that could happen if you do not follow them?
- Do you think people who go online regularly take such issues into account? If not, why not?
The discussion can be taken further by discussing the following:
- Who should have access to my/our data?
- Will/Should the government control how companies use data?
- What if your data is used for good – for finding cures to diseases, for example? Does that change your point of view?
- Can anything online be private?
Finally, check if members of your group are aware of such guidelines or privacy policies in their organisation, workplace or school. Invite them to get a copy if it exists and to review it.
In summary, the group might find it useful and interesting to complete the Digital Privacy Quiz (adapted from NPR’s What’s Your Privacy Personality? quiz).
Activity 4. 2 Exploring our digital footprints

Key Questions
- Why is it important to know the extent of my digital footprint?
- Why is it important to protect my personal information online?
1. Discuss the concept of a digital footprint with the group.
- How might such a footprint (something that reveals your online activity) tell other people about who you are or what interests you?
- How might such information be used positively and/or negatively?
Distribute the How your personal information is tracked, collected and used handout and get the group to review it. Identify what surprises them about how their personal information is tracked, collected and used. How does this make them feel?
Note: explain that our online activities are tracked using a digital tool called a cookie (the term comes from ‘fortune cookie’ because of its embedded message). Cookies are data sent from websites we visit and are stored on a user’s web browser. Normally, they help the website remember the user so they can avoid having to resign in. Cookies also help computers receive information more efficiently. But they also can track searches, cataloging the words used and the sites visited. You can see cookies working when you have shopped online for something and then see ads for the same item on search engines, social media sites or email.
It is important that they also understand that privacy policies can only protect some personal information from being tracked, collected and used by others. Some companies enforce their privacy policies while many others do not. Some online companies don’t even have privacy policies. There are also hackers who can break into secure systems and steal information from emails and databases.
Ask the group if, given all this information, they feel protecting their personal information is their responsibility. Why or why not? How can making smart decisions help reduce the chance of unwanted exposure?
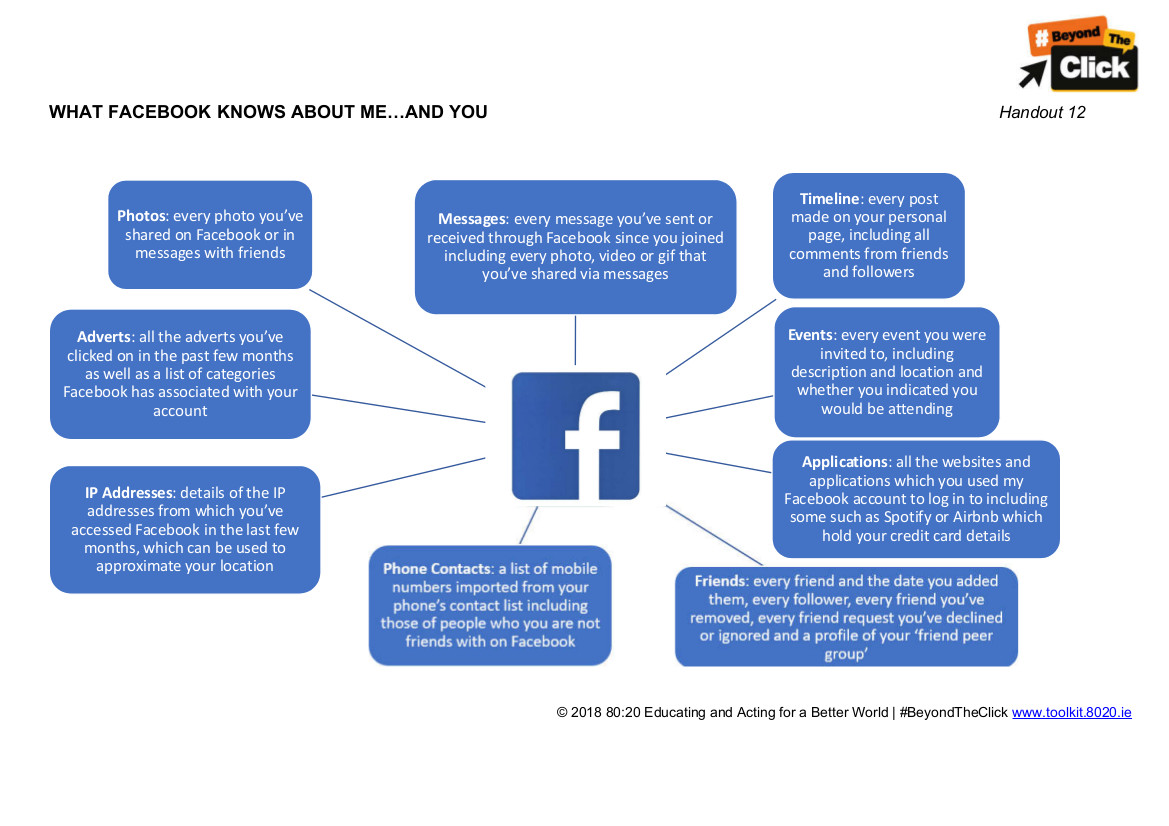
2. Distribute or display the What Facebook knows about me…and you diagram.
- Handout 12: What Facebook knows about me…you – diagram
The diagram records the data available to Facebook based upon any person’s use of the platform. Ask the members of your group,
- Were they aware of the detail included and what surprises or disturbs them?
- Would they want any of this footprint or data to be changed or eliminated? Why?
Activity 4. 3 Protecting Your Digital Footprint
- Handout 13: Ways to protect your digital footprint (adapted from Teaching Tolerance)
Ask them to review the different suggestions for protecting their privacy. Discuss which suggestions make sense and why. Are there any that seem difficult or unnecessary? Why?
Keywords
It might also be useful at some stage in the process to discuss some of the keywords associated with these issues and whether we effectively understand them.
- data – facts and statistics collected together for reference or analysis
- digital footprint – the information available about a person online because of their own digital activity
- cookie – a small piece of data sent from a website and stored on a user’s computer by the user’s web browser while the user is browsing
- privacy policy – a document that explains how an organization handles any customer, client or employee information gathered in its operations
- hacker – a person who circumvents security and breaks into a network, computer, file, etc., usually with malicious intent
- database – a comprehensive collection of related data organized for convenient access, generally in a computer